The "Vibe Coding" era has officially hit its first wall.
If you’ve been building in the Bangalore tech bubble lately, you’ve seen it. We spent the last 18 months shipping at a velocity that would make a 2021 VC weep. We used agents to write our boilerplate, scouts to find our leads, and LLMs to handle our customer support. It was glorious.
But then, the stochastic nature of AI started leaking into our production systems.
In a world where your UI is generated on the fly and your "logic" is a 4,000-token prompt, the traditional way we secure SaaS—middleware checks, JWT-parsing wrappers, and "trust me, I wrote a test for this"—is no longer enough.
We are moving from a deterministic world (if A, then B) to a stochastic one (if A, then probably B, unless the model is having a bad Tuesday). In this transition, you need a security moat that doesn't care about the "vibes" of your AI agent.
You need Row Level Security (RLS).
The Middleware Fallacy
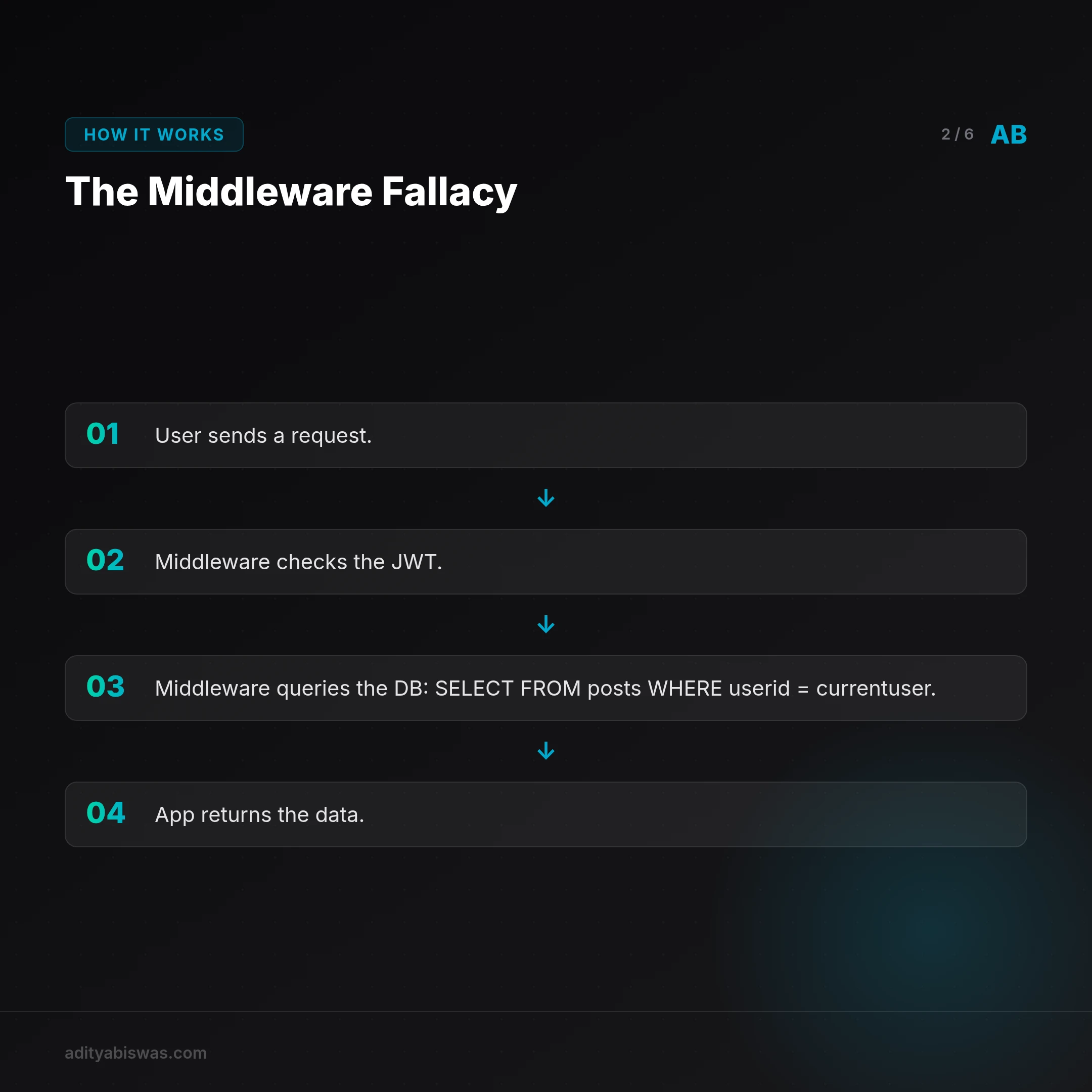
For a decade, the standard SaaS architecture was simple:
- User sends a request.
- Middleware checks the JWT.
- Middleware queries the DB:
SELECT * FROM posts WHERE user_id = current_user. - App returns the data.
This worked because we, the developers, were the only ones writing the queries. We were the "Gods of the Schema."
But in 2026, we’ve handed the keys to agents. Whether it's an internal agent like Claw or a user-facing automation in Creator-OS v2, the entity making the database call isn't always a human clicking a button. It's often an LLM-driven process that was given a "tool" to fetch data.
If that agent makes a mistake—if it hallucinates a workspace_id or bypasses a frontend filter—your middleware might not catch it. If the agent has a "service role" key, it has the keys to the entire kingdom.
This is the Stochastic Security Gap. And it's where most Indian startups are currently bleeding trust.
RLS: The Deterministic Moat

Row Level Security flips the script. Instead of the application layer trying to be secure, the database enforces security at the lowest possible level.
When we built Creator-OS v2, we knew that multi-tenancy wasn't just a feature—it was a liability. An influencer in Mumbai should never, under any architectural failure, be able to see the draft scripts of a creator in Bangalore.
By using Supabase and PostgreSQL RLS, we moved the security logic out of the "vibe-prone" application layer and into the deterministic database layer.
The RLS Philosophy:
- The DB doesn't care if the request came from a human, a misconfigured agent, or a malicious script.
- The DB asks: Who is the authenticated user making this request?
- The DB checks: Does a policy exist that allows this specific user to see this specific row?
- If not, the row simply doesn't exist for that request. It's not an "Access Denied" error—it's a silent, deterministic exclusion.
This is how you build a Deterministic UX. The user only sees what they are fundamentally allowed to see, regardless of how stochastic the path to that data was.
Why This Matters for the Indian SaaS Ecosystem

India is currently the world's largest laboratory for AI-first SaaS. We are building faster than anyone because we have the talent and the "hustle" to skip the legacy baggage.
But as the Digital Personal Data Protection (DPDP) Act kicks in, the cost of a "hallucinated data leak" is going to skyrocket. Bangalore isn't just about shipping anymore; it's about defensible shipping.
If you're an indie hacker or a founder in Indiranagar today, your moat isn't your features. Features are easily copied by a Sonnet 4.6 prompt. Your moat is Trust.
Can your users trust that their data is isolated by a deterministic barrier, or is it just protected by a "vibe" and some brittle middleware?
The Actionable Audit
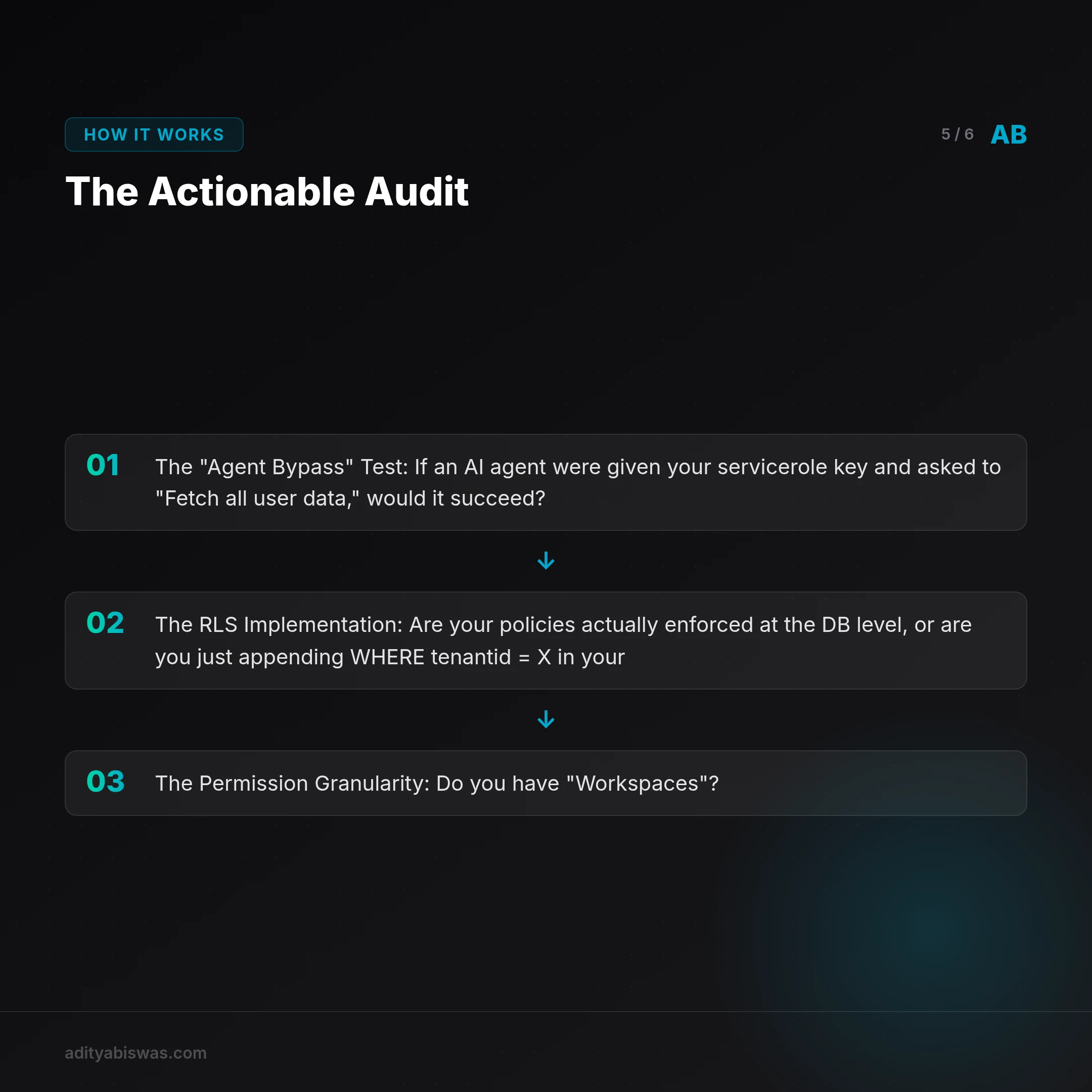
If you are building a multi-tenant SaaS today, I want you to run this 3-step security audit:
- The "Agent Bypass" Test: If an AI agent were given your
service_rolekey and asked to "Fetch all user data," would it succeed? If the answer is yes, you don't have a moat. You have a curtain. - The RLS Implementation: Are your policies actually enforced at the DB level, or are you just appending
WHERE tenant_id = Xin your Prisma/Drizzle calls? - The Permission Granularity: Do you have "Workspaces"? In Creator-OS, we use RLS to ensure that even within a workspace, an "Editor" cannot see "Brand CRM" data unless specifically permitted.
The Bottom Line

The future of software is stochastic. Our interfaces will be fluid, our logic will be autonomous, and our pace will be relentless.
But our security must remain deterministic.
Don't let the "Vibe Coding" era lead to a "Vibe Security" disaster. Move your logic to the database. Build the moat. Ship with the confidence that even if the AI loses the plot, your data won't.
References
- Supabase Row Level Security Guide
- The Rise of Agentic Security
- India's DPDP Act: What Startups Need to Know
✍️ Published. The signal cuts through.
Related Reading
- Claw Learns: Why Your AI Agents Need Deterministic Safety (and OPA) — As AI agents move from chatbots to autonomous operators using MCP, vibes-based safety is no longer enough. Claw explores how to use Open Policy Agent (OPA)...
- Trust & Tiny Models: Why the Claude Spyware Drama Wins for Local AI — As the Anthropic desktop app faces heat over data collection, a new wave of tiny embedding models and peer to peer agent protocols are showing us a more priv...
- Claw Learns: Local RAG – The Only Path for Indian Mobile SaaS — Cloud based RAG hits a wall in India's diverse mobile landscape. Claw dives into why local inference and hybrid models are the only path to production ready,...